Difference: TWikiAccessControl (43 vs. 44)
Revision 442017-08-09 - TWikiContributor
TWiki Access ControlRestricting read and write access to topics and webs, by Users and groups TWiki Access Control allows you restrict access to single topics and entire webs, by individual user and by user Groups. Access control, combined with TWikiUserAuthentication, lets you easily create and manage an extremely flexible, fine-grained privilege system.On this page:
An Important Control ConsiderationYour organization will learn that, while fostering an open collaborative environment, soft security (peer review), together with version control (complete audit trail) will take care of any security concern you might have. Open, free-form editing is the essence of WikiCulture - what makes TWiki different and often more effective than other collaborative environments. For that reason, it is strongly recommended that decisions to restrict read or write access to a web or a topic are made with great care - the more restrictions, the less wiki in the mix. Experience shows that unrestricted write access works very well because:
Permissions settings of the webs on this TWiki site
Authentication vs. Access ControlAuthentication: Identifies who a user is based on a login procedure. See TWikiUserAuthentication. Access control: Restrict access to content based on users and groups once a user is identified.Users and GroupsAccess control is based on the familiar concept of Users and Groups. Users are defined by their WikiNames. They can then be organized in unlimited combinations by inclusion in one or more user Groups. For convenience, Groups can also be included in other Groups.Managing UsersA user can create an account in TWikiRegistration. The following actions are performed:
Managing GroupsThe following describes the standard TWiki support for groups. Your local TWiki may have an alternate group mapping manager installed. Check with your TWiki administrator if you are in doubt. Groups are defined by group topics located in theMain web. To create a new group, visit TWikiGroups and enter the name of the new group ending in Group into the "new group" form field. This will create a new group topic with two important settings:
The Super Admin GroupA number of TWiki functions (for example, renaming webs) are only available to administrators. Administrators are simply users who belong to the SuperAdminGroup. This is a standard user group, the name of which is defined by {SuperAdminGroup} setting in configure. The default name of this group is theTWikiAdminGroup. The system administrator may have chosen a different name for this group if your local TWiki uses an alternate group mapping manager but for simplicity we will use the default name TWikiAdminGroup in the rest of this topic.
You can create new administrators simply by adding them to the TWikiAdminGroup topic. For example,
| |||||||||||||||||||||||||
| Added: | |||||||||||||||||||||||||
| > > | On a large TWiki installation having hundreds or thousands of webs, a single super admin group may not be able to take care of all of those webs. One way to deal with that is to have a super admin group for each web. AutonomousWebs shows how to. | ||||||||||||||||||||||||
Restricting AccessYou can define who is allowed to read or write to a web or a topic. Note that some plugins may not respect access permissions.
Controlling access to a WebYou can define restrictions on who is allowed to view a TWiki web. You can restrict access to certain webs to selected Users and Groups, by:
ALLOWWEBVIEW set, this will also apply to the subweb. Also note that you will need to ensure that the parent web's FINALPREFERENCES does not include the access control settings listed above. Otherwise you will not be able override the parent web's access control settings in sub-webs.
Creation and renaming of sub-webs is controlled by the WEBCHANGE setting on the parent web (or ROOTCHANGE for root webs). Renaming is additionally restricted by the setting of WEBRENAME in the web itself.
Note: If you restrict access to the Main, make sure to add the TWikiRegistrationAgent so that users can register. Example:
Controlling access to a Topic
| |||||||||||||||||||||||||
| Added: | |||||||||||||||||||||||||
| > > | You may want to allow or deny access to a topic in addition to the ALLOWEB* or DENYWEB* specifies. In that case having + as the first non-space character of ALLOWTOPIC* or DENYTOPIC* has that effect.
For example, the following setting allows view by MarketingExecGroup in addition to the people ALLOWWEBVIEW allows.
| ||||||||||||||||||||||||
See "How TWiki evaluates ALLOW/DENY settings" below for more on how ALLOW and DENY interacts.
Allowing public access to specific topics in a restricted webYou may want to completely open up access to a specific topic within a restricted web - allowing access by anybody. There is a special group for that - Main.AllUsersGroup. The following setting allows view access to the topic by anybody even if they are not authenticated.
tools/eliminate_emptydenytopic is provided.
After upgrading from pre 6.0 to post 6.0, you need to run it.
Empty values in access control variablesSetting an empty value to an access control variable is the same as not setting at all:
Securing File AttachmentsBy default, TWiki does not secure file attachments. Without making the following changes to the twiki.conf file, it is possible for anyone who has access to the server to gain access to an attachment if they know the attachment's fully qualified path, even though access to the topic associated with the attachment is secured. This is because attachments are referred to directly by Apache, and are not by default delivered via TWiki scripts. This means that the above instructions for controlling to topics do not apply to attachments unless you make the changes as described below. An effective way to secure attachments is to apply the same access control settings to attachments as those applied to topics. This security enhancement can be accomplished by instructing the webserver to redirect accesses to attachments via the TWikiviewfile script, which honors the TWiki access controls settings to topics. See the notes below for implications.
The preferred method to secure attachments is by editing the twiki.conf file to include:
ScriptAlias /do /filesystem/path/to/twiki/bin
Alias /pub/TWiki /filesystem/path/to/twiki/pub/TWiki
Alias /pub/Sandbox /filesystem/path/to/twiki/pub/Sandbox
ScriptAlias /pub /filesystem/path/to/twiki/bin/viewfile
Notes:
Controlling who can manage top-level websTop level webs are a special case, because they don't have a parent web with a WebPreferences. So there has to be a special control just for the root level.
ROOTCHANGE access to rename an existing top-level web. You just need WEBCHANGE in the web itself.
How TWiki evaluates ALLOW/DENY settingsWhen deciding whether to grant access, TWiki evaluates the following rules in order (read from the top of the list; if the logic arrives at PERMITTED or DENIED that applies immediately and no more rules are applied). You need to read the rules bearing in mind that VIEW, CHANGE and RENAME access may be granted/denied separately.
| |||||||||||||||||||||||||
| Changed: | |||||||||||||||||||||||||
| < < | Allowing web creation by user mapping manager | ||||||||||||||||||||||||
| > > | Allowing web creation/deletion/rename by user mapping manager | ||||||||||||||||||||||||
| Changed: | |||||||||||||||||||||||||
| < < | There are cases where DENYROOTCHANGE, ALLOWROOTCHANGE, DENYWEBCHANGE, and ALLOWWEBCHANGE, and DENYWEBCHANGE are not capable enough to implement web creation permission you want.
To cope with such cases, when a new web is created, the canCreateWeb($cUID, $web) method of the user mapping manager is called if the method exists. | ||||||||||||||||||||||||
| > > | There are cases where DENYROOTCHANGE, ALLOWROOTCHANGE, DENYWEBCHANGE, and ALLOWWEBCHANGE, and DENYWEBCHANGE are not capable enough to implement web creation and rename permissions you want.
To cope with such cases, when a new web is created, the canCreateWeb($cUID, $web) method of the user mapping manager is called if it exists. | ||||||||||||||||||||||||
| If it returns true, TWiki goes ahead and create the web without checking access control variables. | |||||||||||||||||||||||||
| Added: | |||||||||||||||||||||||||
| > > | Similarly, when a web is renamed (deletion is a form of rename), the canRenameWeb($cUID, $oldWeb, $newWeb) method of the user mapping manager is called if it exists. | ||||||||||||||||||||||||
Please read AllowWebCreateByUserMappingManager for more details.
Forbid certain users to do certain actions by configurationYou may have an unruly registered users (e.g. a crawler program) who don't follow the rules while you don't have control over such users. And the web application container in which TWiki is installed may be managed by somebody else and you don't have tight and quick control. To cope with such situations, certain users can be forbidden certain scripts by setting{ForbidUserAction}.
A good example is worth more than a lengthy explanation, so here it is:
$TWiki::cfg{ForbidUserAction} = '
AggresiveCrawler: edit, oops, search;
ReadOnlyUser: !view, viewfile;
TotallyForbidden: !nothing;
';
In this example:
User masqueradingThere are cases where it's handy to access TWiki on behalf of somebody else retaining a trace of your real identity rather than completely becoming a different user. We call it user masquerading. TWiki provides a framework to implement that. Please read UserMasquerading for more information. This is an advanced feature and not many TWiki sites are using, but there is a part in the following section mentioning it, it's mentioned here.Dynamic access controlThere are pitfalls and you need to harden your web to avoid unexpected access. Before using this feature, please read this entire section through carefully. You may want to restrict access dynamically -- based on topic name, a form field value, or some combination of factors. To cope with such situations, the dynamic access control mechanism is provided. If you setDYNAMIC_ACCESS_CONTROL 'on' at WebPreferences of the web, TWiki variables in access control variables mentioned above are expanded.
Example 1 - restriction based on topic nameLet's assume you need to restrict changes only to the CroniesGroup members except with topics whose name ends with Public, which need be changed by anybody. That is achieve by the following settings on WebPrefences.
* Set DYNAMIC_ACCESS_CONTROL = on
* Set ALLOWWEBCHANGE = %IF{"'%CALCULATE{$SUBSTRING(%TOPIC%, -6, 6)}%' = 'Public'" then="%WIKINAME%" else="CroniesGroup"}%
Example 2 - restriction based on form fieldLet's assume:
* Set DYNAMIC_ACCESS_CONTROL = on
* Set ALLOWWEBVIEW = %IF{"'%CALCULATE{$SUBSTRING(%TOPIC%, 1, 6)}%' = 'ReqEnt' and '%FORMFIELD{Requestor}%' != '%WIKINAME%'" then="SupportGroup" else="%WIKINAME%"}%
Specifically the following access control variables are subject to TWiki variable expansion in their values.
Dynamic access control in accessing a different web's topicLet's assume WebA has the following lines on WebPreferences.* Set DYNAMIC_ACCESS_CONTROL = on * Set MEMBERS = JaneSmith, JoeSchmoe * Set ALLOWWEBVIEW = %MEMBERS%This is not a good way to use dynamic access control but it does restrict access only to those listed in MEMBERS. However, access control doesn't work as expected when WebA.TopicB is accessed from WebC.TopicD by %INCLUDE{WebA.TopicB}% or other variables.
This is because %MEMBERS% is defined in WebA and may have a different value in other webs.
You may think the following lines cheat the access control on WebA but actually not.
* Set MEMBERS = %WIKINAME%
%INCLUDE{WebA.TopicB}%
This is because when a topic (e.g. WebC.TopicD) is accessed from browser and the topic refers to another topic in a different web (e.g. WebA.TopicB) and the different web employs dynamic access control, access to another topic is defined being on the safer side.
Topic level dynamic access controlOn a topic, it's possible to use a variable defined on the topic for topic level access restriction. E.g.* Set MEMBERS = JaneSmith, JoeSchmoe * Set ALLOWTOPICVIEW = %MEMBERS%[This is not a good way to use dynamic access control Dynamic access control and user masqueradingYour user mapping handler may be providing the UserMasquerading feature. In that case, you expect dynamic access control to just work when user masquerading is in effect. Otherwise, you cannot test if your dynamic access control configuration is working as expected on your own. Dynamic access control does work as expected even if user masquerading is in effect. For that, the following things are happening under the hood. Let's think about Example 2 mentioned above. When you masquerading as SomebodyElse, you need to be able to see SomebodyElse's requests only. In the access control setting, a form field value is compared with %WIKINAME%. While user masquerading is in effect, your wiki name is YourNameOnBehalfOfSomebodyElse. It cannot match the form field value. To make dynamic access control work under these circumstances, variable expansion for dynamic access control is skewed as follows. Specifically, the following variables are expanded to the value of SomeboyElse's rather than YourNameOnBehalfOfSomebodyElse's.
Avoiding vulnerabilityBy default, user level preferences are read before web level preferences. This means a user can set a preferences variable at the user level and finalise it. To prevent this sort of attack, you need to harden your web or site by disabling user preferences by e.g. having the following line onlib/LocalSite.cfg
$TWiki::cfg{DemoteUserPreferences}= 1;
and having the following line on your WebPreferences and then finalise DENYUSERPREFEENCES.
* Set DENYUSERPREFEENCES = allPlease read TWikiVariables#ControllingUserLevelPrefsOverride for details. Again by default, predefined variables such as %IF{...}% can be overridden by preferences variables.
If user preferences are disabled, ordinary users cannot attack using user preferences, but topic level preferences may cause unexpected consequences.
As such, all predefined variables need to be made un-overridable by having the following line on WebPreferences and then finalise OVERRIDABLEPREDEFINEDVARIABLES.
* Set OVERRIDABLEPREDEFINEDVARIABLES =Please read TWikiVariables#PredefinedVariables for details. Disabling dynamic access controlYou may not be comfortable with dynamic access control because it may slow things down. Or you may not want to be bothered by questions raised by users about it. If so, you can disable it by setting DYNAMIC_ACCESS_CONTROL 'off' and then finalizing at the local site level. (cf. TWikiVariables#Setting_Preferences_Variables)Access control and INCLUDEALLOWTOPICVIEW and ALLOWTOPICCHANGE only applies to the topic in which the settings are defined. If a topic A includes another topic B, topic A does not inherit the access rights of the included topic B. Examples: Topic A includes topic B
Customizing "access denied" messageWhen access is denied, a page as follows is displayed: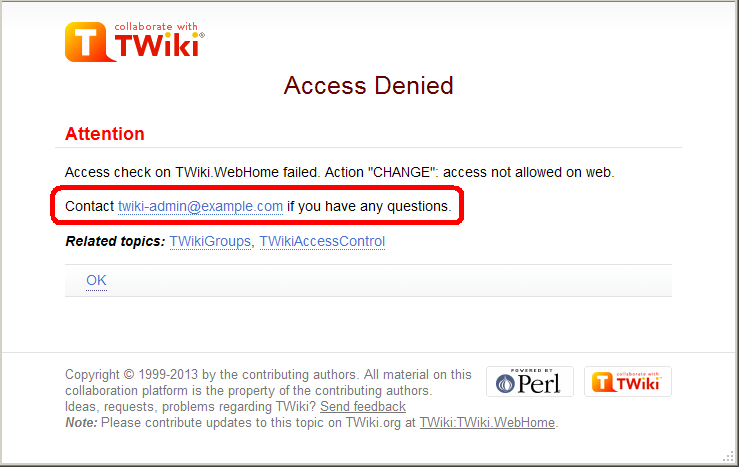 You may want to customize the passage annotated in the red rectangle.
For example, with a web restricting access, you may want to show the link to an access request form.
You can achieve that by setting
You may want to customize the passage annotated in the red rectangle.
For example, with a web restricting access, you may want to show the link to an access request form.
You can achieve that by setting TOPIC_ACCESS_CONTACT varialbe on WebPreferences. e.g.
* Set TOPIC_ACCESS_CONTACT = If you need to access this site, please apply [[Main.AccessForm][here]]Please note that setting it on a topic other than WebPreferences does not take effect. This is a limitation of the current implementation. Custom user/group notationsYou can have custom user/group notations such asUSER:userid and LDAPGROUP:group-name and use them for access control. For example:
* Set ALLOWWEBCHANGE = USER:buzz, LDAPGROUP:foo-barIn a large organization, TWiki may need to depend on user and group data provided by its infrastructure. Custom user/group notations are handy in such situations though it's not trivial to implement. Please read here for details. Access Control quick recipesRestrict Access to Whole TWiki SiteIn a firewalled TWiki, e.g. an intranet wiki or extranet wiki, you want to allow only invited people to access your TWiki. There are three options: 1. Install TWiki Behind Firewall: The firewall takes care of giving access to TWiki to authorized people only. This is a typical setup for a company wiki. As for TWiki configuration, no special setup is needed. 2. Extranet TWiki Using Template Login: All TWiki content (pages and attachments) need to be access controlled. The Template Login allows users to login and logout. Only logged in users can access TWiki content. Configuration: Follow the default setup, then change these configure settings:
twiki/bin and twiki/pub directories to all but valid users. In the Apache config file for TWiki (twiki.conf or .htaccess), replace the <FilesMatch "(attach|edit|... section with this:
<FilesMatch ".*">
require valid-user
</FilesMatch>
Notes:
Authenticate and Restrict Selected Webs OnlyUse the following setup to provide unrestricted viewing access to open webs, with authentication only on selected webs. Requires TWikiUserAuthentication to be enabled.
Hide Control SettingsEdit topic preference settings under More topic actions menu. Preferences set in this manner are not visible in the topic text, but take effect nevertheless. Access control settings added as topic preference settings are stored in the topic meta data and they override settings defined in the topic text.
Alternatively, place them in HTML comment markers, but this exposes the access setting during ordinary editing.
Obfuscating WebsAnother way of hiding webs is to keep them hidden by not publishing the URL and by preventing theall webs search option from accessing obfuscated webs. Do so by enabling the NOSEARCHALL variable in WebPreferences:
Read-only Skin ModeIt is possible to turn the PatternSkin and TopMenuSkin into read-only mode by removing the edit and attach controls (links and buttons). This is mainly useful if you have TWiki application pages or dashboards where you do not want regular users to change content. The read-only skin mode is not a replacement for access control; you can use it in addition to access control. Details at PatternSkinCustomization#ReadOnlySkinMode.Configuring access control for topics of a certain name in all websYou may need to restrict access to topics of a certain name in all webs. For example, there might be an add-on refering to a certain topic of all webs. And the add-on does things only administrators are supposed to do. In that case, change to the topic needs to be restricted only to administrators and must not be overridable. Let's say there is AutomationAddOn which refers to WebAutomation of all webs. And WebAutomation needs to be modifable only by administrators. That can be achieved by the following configuration.
$TWiki::cfg{Access}{Topic}{WebAutomation} = {
DENYCHANGE => 'Main.AllUsersGroup',
};
In addition to ALLOWCHANGE, you can sepcify DENYCHANGE, ALLOWVIEW, DENYVIEW, ALLOWRENAME, and DENYRENAME as follows.
$TWiki::cfg{Access}{Topic}{SpecialTopic} = {
DENYVIEW => 'JoeSchmoe',
ALLOWVIEW => 'FooGroup',
};
$TWiki::cfg{Access}{Topic}{TOPICNAME} has precedence over DENYTOPIC* and ALLOWTOPIC*.
For example, if the configuration for WebAutomation is there as above, there is no way to allow non-adminsitrators to change the WebAutomation topic of any web.
As a way to configure access control, this may look crude.
The reason why configured this way is that this can be part of plugin/add-on/contrib's configuration.
For example, Config.spec of AutomationAddOn would have the following lines, with which proper access control to WebAutomation topics is implemented without the administrator knowing it.
$TWiki::cfg{Access}{Topic}{WebAutomation} = {
DENYCHANGE => 'Main.AllUsersGroup',
};
| |||||||||||||||||||||||||
| Changed: | |||||||||||||||||||||||||
| < < | Related Topics: AdminDocumentationCategory, TWikiUserAuthentication, AllowWebCreateByUserMappingManager, UserMasquerading, CustomUserGroupNotations, TWiki:TWiki.TWikiAccessControlSupplement | ||||||||||||||||||||||||
| > > | Related Topics: AdminDocumentationCategory, TWikiUserAuthentication, AllowWebCreateByUserMappingManager, AutonomousWebs, UserMasquerading, CustomUserGroupNotations, TWiki:TWiki.TWikiAccessControlSupplement | ||||||||||||||||||||||||
-- Contributors: TWiki:Main.PeterThoeny
| |||||||||||||||||||||||||
View topic | History: r44 < r43 < r42 < r41 | More topic actions...
Ideas, requests, problems regarding TWiki? Send feedback
Note: Please contribute updates to this topic on TWiki.org at TWiki:TWiki.TWikiAccessControl.